Key information
Starting March 15, 2026, SSL/TLS certificates will have shorter maximum validity periods. This change will be implemented in stages: the limit will be reduced to 200 days in 2026, 100 days in 2027, and finally to 47 days on March 15, 2029. This change applies to all SSL/TLS products.
Important: The certificates offered by Tuthost remain unchanged. However, the individual certificates issued as part of these products must comply with the validity periods in effect at the time of issuance.
This means that certificates will need to be renewed (reissued) more often. To avoid service interruptions, organizations will increasingly rely on automated certificate issuance and renewal.
Note: As part of the implementation of this regulation, the maximum validity of SSL certificates starting from March 13, 2026 will be 199 days.
Key dates
| March 15, 2026 | March 15, 2027 | March 15, 2029 | |
| Period of reuse of data on verification of the subject’s identification information | 398 days | ||
| Maximum validity period of the certificate | 200 | 100 | 47 |
| Maximum period of domain validation reuse | 200 | 100 | 10 |
How to prepare?
Organizations should start preparing now to ensure business continuity. Manual certificate processing will quickly become inefficient and risky, especially if certificates are limited to 100 days or less.
Recommended actions include:
- Train your teams – make sure IT staff understand the timeline, requirements, and practical implications of these changes.
- Know about all certificates – conduct a thorough inventory of every SSL/TLS certificate used on your systems, including websites, backend services, APIs, load balancers, devices, and applications.
- Implement monitoring – set up automatic notifications when a certificate expires. Ensure that notifications reach the right people and provide enough time to take corrective action.
- Automation of the certificate lifecycle – implementation of automated mechanisms for issuing and renewing certificates (e.g., ACME protocol). Certificates with short validity periods will require reliable automation to prevent failures.
- Evaluate your processes – review existing procedures, test automated processes, and eliminate any approval delays or infrastructure bottlenecks.
- Identify systems that can’t yet support automation – plan how to update or replace legacy systems that rely on manual certificate management.
- Make sure your contact email address is valid and monitored – Certum sends renewal notifications and expiration reminders to this address. With shorter certificate validity periods, missing these notifications increases the risk of unexpected failures.
Important: Most organizations need several months to implement automation effectively. Starting early helps to avoid disruptions.
What will happen to SSL/TLS certificates after the transition?
Certificates issued before each key date will remain valid until their expiration date. The issue date (not the order date) determines the expiration date. Processing times for OV and EV certificate applications may vary, so plan your renewals in advance to ensure smooth operations.
After each key date, new certificates will correspond to the updated validity periods:
- until March 13, 2026, valid for up to 398 days,
- between March 13, 2026 and March 15, 2027, valid for up to 200 days,
- between March 15, 2027 and March 15, 2029, valid for up to 100 days,
- after March 15, 2029, valid for up to 47 days.
If the issued certificate has a shorter validity period and expires before your product expires, you can use the reissue process to take full advantage of the validity period available for your product.
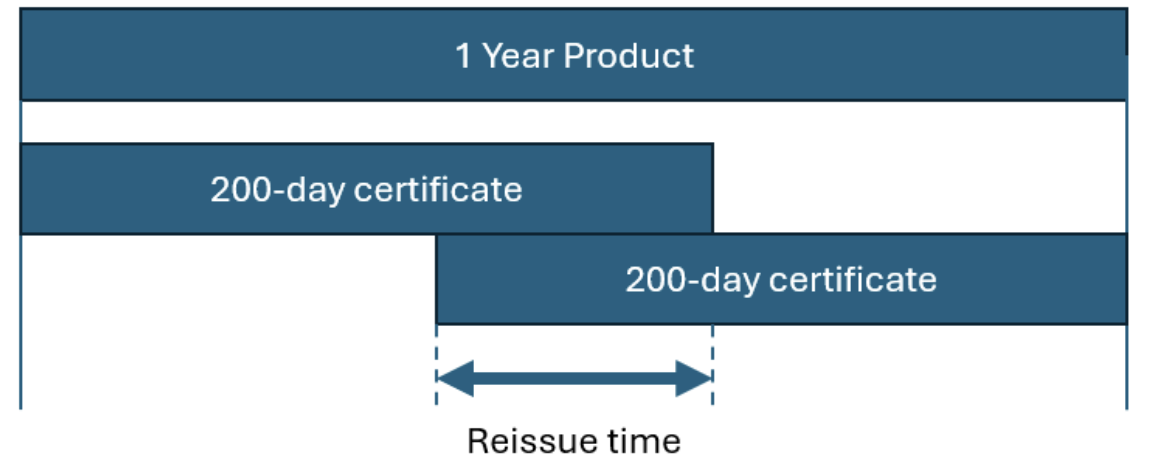
Example: If you purchase a 1-year SSL product and the certificate is issued on March 13, 2026, it will be valid for 200 days. To use the full year of your product, simply re-issue the certificate once between the 165th and 200th day – this will provide you with full coverage for the entire year, divided into two certificates.
When any certificate is reissued after March 15, 2026, the new certificate must comply with the expiration date restrictions in effect on the date of reissuance.
Domain validation reuse periods are also reduced along with certificate expiration dates. This means that when you reissue a certificate, you may need to re-validate the domain if the previous validation has expired. Plan your reissue accordingly to avoid delays.
Why is this changing?
These changes, approved by the CA/Browser Forum in in bulletin SC-081v3 are designed to improve the security and reliability of digital identities on the Internet.
The main reasons include:
- Increased security – shorter validity periods allow for more frequent key rotation, reducing the risk of compromised keys.
- Faster adoption of new standards – frequent updates facilitate faster implementation of updated cryptographic algorithms and security standards.
- Reduced vulnerability period – attackers have less time to misuse a compromised or incorrectly issued certificate.
- Simplified revocation – shorter validity periods reduce reliance on complex revocation systems, as compromised certificates expire faster.
- Improved operational security – more frequent updates reduce the risk of outdated configurations and limit the impact of human error.
- Reliability of certificate information – certificate data is checked more often, which ensures its accuracy and reliability.
Who will suffer the most?
- Organizations with a large number of certificates, especially those without a centralized management process.
- Teams that rely on manual updates, spreadsheets, or email reminders.
- Environments that use short-lived infrastructure such as microservices, containers, or dynamic cloud workloads.
- Companies providing customer-focused services with strict uptime requirements (banks, SaaS, telecommunications, e-commerce).
- Organizations with multiple brands or domains where updates are distributed across different teams.
- Outdated systems that do not support automatic certificate renewal.
